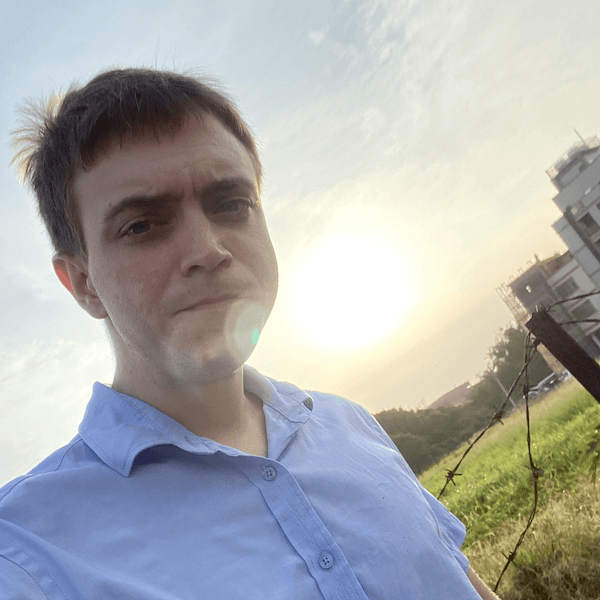
 Jonathan Nichols
Jonathan Nichols
whoami
My name is Jonathan Nichols and I am a part-time penetration tester and bug bounty hunter. I have been working in cyber security for about three years. I am originally from New York and I currently live in Taiwan where I have been an English teacher for seven years.Profile on Hackrate
Profiles on Social Media
First steps in bug hunting
How did you get into bug bounty hunting?
I first entered the cyber security space when I signed up for the OSCP exam. After I passed the exam, I learned about bug bounty and decided to give it a shot in order to continue to improve my skills.
Hacker insight
As for advice for beginners, the most important tip is to not give up. It may sound cliché, but in my case I hacked for five months straight before finding my first bug. Another important thing to remember is to try to focus on one target for at least a few days before moving on. There are so many targets to choose from, so when you don't find a bug in a few hours, it's very tempting to just try another target/website. But, if you stay on the target after you think there's nothing left to find, that is when you will find something interesting because that's where others have given up.
About the testing methodology
Do you follow a pre-defined methodology or do you prefer to change your methods regularly?
As far as my testing methodology, I like to keep it pretty traditional. I will use the application as intended for a while until I get a feel for all of the functions. Eventually, I will start to find things that I can possibly be exploited such as file upload or password reset features. After I have exhausted this step I will always go check my Burp history for interesting endpoints/parameters.
Do you have any favorite tool or favorite wordlist to test with?
As I mentioned above I use Burp Suite a lot. I also love to use the tool gau as well as the wayback machine website. A huge amount of the bugs I have found have been a direct result of these tools.
Favorite bug classes
Do you have any favorite vulnerabilities to focus on during testing?
My favorite bug type is definitely SSRF. When checking my Burp history and the wayback machine, I always keep an eye out for GET/POST parameters that have a URL as a value such as http://website/file?url=http://example I am often able to change the URL to an internal IP address and retrieve internal data.
Certifications and Achievements
Do you have any security certificates? How important do you think certifications are nowadays?
I currently have the OSCP certification. In my opinion, getting certifications can be a great way to motive yourself to learn. If it wasn't for the OSCP, I never would have pushed myself to learn how to hack and I would never know how much I enjoy it. However, I do think that some certifications are not practical enough and are only really good for getting a job interview.
Future of bug bounty
I have seen the types of bugs that come out of bug bounty and I can say for sure that bug bounty will only grow in the future. The motivation to earn bounties makes researchers push way harder than they would on traditional penetration tests. As a result, some extremely creative and serious vulnerabilities are found that would otherwise not have been reported and fixed.
What is your impression of HACKRATE?
I feel very comfortable working on the Hackrate platform and the team has been very positive and helpful. The bug triaging process can be tricky when researchers and triagers don't agree, but the Hackrate team has been a pleasure to work with.
Badges

Newcomer
6/25/2021
Bounty_Hunter
6/25/2021